Where to start with PQC migration
Discover cryptographic assets and quantum vulnerabilities. Build complete inventories, assess exposure, receive mitigation steps.
Helping telecommunications and network operators "Detect, Protect and Comply" as they modernise encryption and prepare for quantum risk.
If you're thinking about how to stay ahead of emerging threats, we’re here to help, especially if you're grappling with challenges like:
Discover cryptographic assets and quantum vulnerabilities. Build complete inventories, assess exposure, receive mitigation steps.
Secure data in transit with quantum-safe symmetric key agreement. Deploy SKA-Platform and SKA-EC for scalable, standards-based encryption across networks and edge.
Arqit and Intel are working together to help organisations benefit from AI-assisted network safety, and provide genuine, end-to-end sovereignty for enterprise customers.
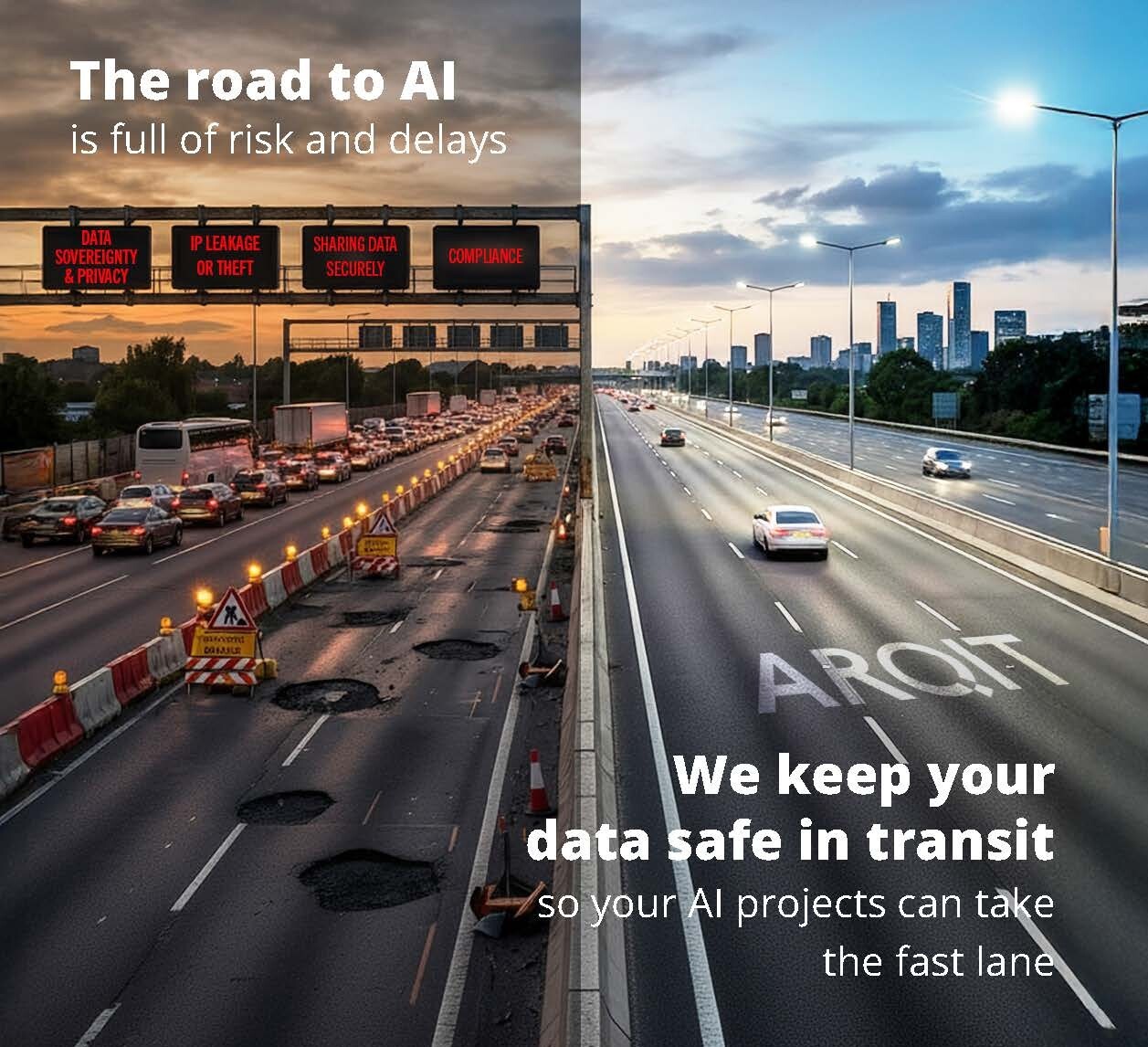
In the latest MWL AI Report 2026*, 62% of respondents cited Data Sovereignty and Privacy as the factor slowing down their AI security projects in the public cloud.
Arqit and Intel are working together to deliver genuine, end to end sovereignty for enterprise.
*Mobile World Live interviewed over 200 global IT and security leaders in their latest report.
Discover cryptographic assets and quantum vulnerabilities. Build complete inventories, assess exposure, receive mitigation steps.
Secure data in transit with quantum-safe encryption keys.
Meet evolving standards and government guidance. Evidence controls, demonstrate progress, support NIST and FIPS compliance.
Arqit delivers quantum-resistant encryption through Symmetric Key Agreement (SKA), Encryption Intelligence for cryptographic discovery, and NetworkSecure for data-in-transit protection—purpose-built for telecom and network operators preparing for post-quantum threats.
We enable telecom operators to Detect cryptographic vulnerabilities through continuous network assessment, Protect data with quantum-safe symmetric encryption, and Comply with evolving NIST and NSA standards—reducing quantum risk while maintaining operational continuity across legacy and modern infrastructure.
Yes. Our software-only approach integrates with existing network architectures, OEM devices, and orchestration platforms without requiring hardware replacement. Each deployment is configured to your specific threat profile, compliance requirements, and operational constraints, ensuring seamless adoption at scale.
Yes. Encryption Intelligence continuously monitors your cryptographic estate, providing real-time visibility into encryption usage, vulnerability exposure, and quantum readiness. You receive detailed assessments with mitigation recommendations, compliance evidence, and progress tracking against your post-quantum migration roadmap.
Arqit uses patented Symmetric Key Agreement instead of vulnerable public key infrastructure, delivering quantum-safety today. Our software-only, standards-based platform offers cryptoagility, zero-trust authentication, and split-trust architecture - ensuring high security with low operational overhead, formal protocol verification, and proven compliance with FIPS, NIST, and CSfC requirements.